AI‑driven attack automation meets integrated intel 🌐. Act now to fortify critical assets 🛡️.
Good morning, March 12 2026 – here’s the latest cyber and AI threat intelligence.
Today's headlines
- GreyNoise integrates with Google SecOps for instant malicious IP blocking.
- GreyNoise now powers CrowdStrike Falcon threat intel.
- Default admin credentials on IoT devices remain a high‑impact risk.
- Microsoft Authenticator may leak login codes, prompting urgent updates.
- OpenClaw AI skills are being weaponized to deliver large‑scale malware.
1️⃣ New GreyNoise‑Google SecOps Integration Boosts Threat Detection
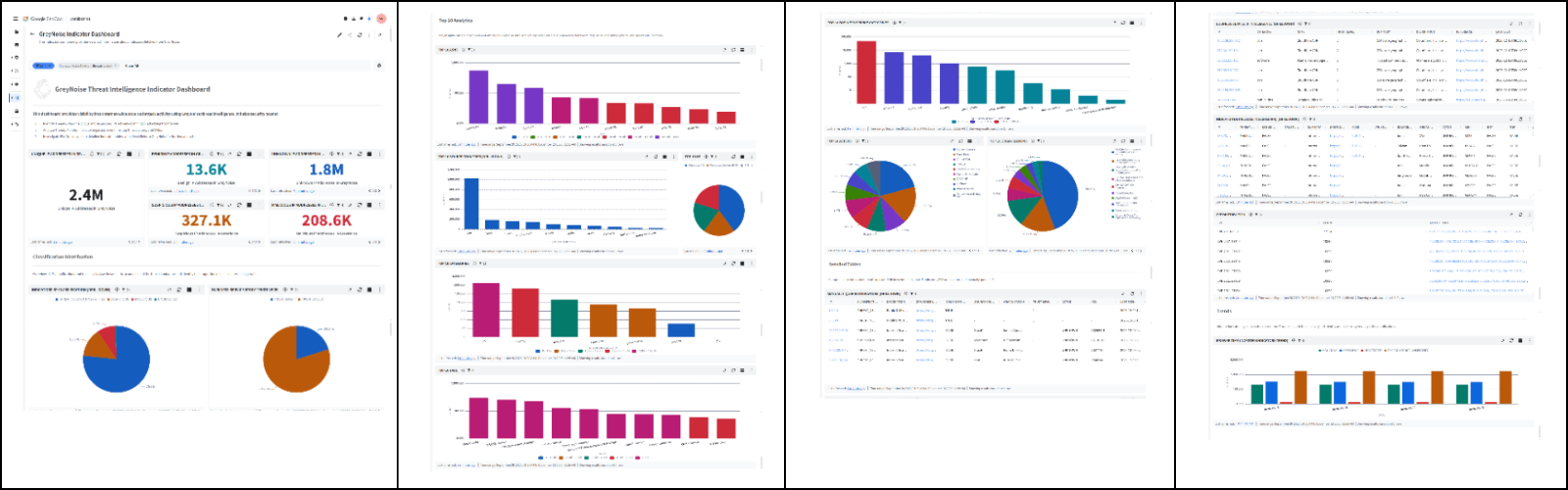
Key Points:
- Configurable real‑time blocklists block malicious IPs instantly.
- Adds context to alerts, filtering noisy internet‑scanner traffic.
- Enables automated response workflows in Google Cloud environments.
- Improves SOC efficiency for small and mid‑size enterprises.
Description:
GreyNoise announced a native integration with Google SecOps that delivers real‑time, customizable blocklists directly into Google Cloud security pipelines, allowing teams to suppress low‑value noise and focus on genuine threats.
Why It Matters:
By reducing false‑positive alerts and automating blocklist enforcement, organizations can accelerate incident response, lower SOC fatigue, and protect critical workloads from active reconnaissance and exploitation.
2️⃣ GreyNoise Intelligence Now Embedded in CrowdStrike Falcon Platform
Key Points:
- CrowdStrike Falcon users receive GreyNoise context on malicious IP activity.
- Supports threat hunting and vulnerability prioritization.
- Provides early warning for emerging exploit trends.
- Streamlines investigation by correlating Falcon detections with GreyNoise data.
Description:
The partnership extends GreyNoise’s IP reputation and activity data into the CrowdStrike Falcon suite, giving analysts enriched intelligence at the point of detection for faster decision‑making.
Why It Matters:
Integrating reputable external intel reduces investigation time, helps prioritize remediation of exploited assets, and strengthens overall breach detection capabilities across enterprise environments.
3️⃣ IoT Devices Using Default Admin Credentials Remain Critical Risk

Key Points:
- Default admin passwords on IoT hardware are still widely deployed.
- Attackers can gain persistent privileged access within minutes.
- Strong, unique credentials and MFA are recommended mitigations.
- Continuous device fingerprinting and monitoring improve detection.
Description:
A SANS diary entry highlights recent incidents where IoT devices logged in with default administrator accounts, allowing attackers to bypass defenses and maintain long‑term footholds in networks.
Why It Matters:
Compromised IoT devices can serve as entry points for lateral movement and data exfiltration; securing credentials is a low‑cost, high‑impact control for protecting operational technology environments.
4️⃣ Microsoft Authenticator Vulnerability May Expose Login Codes

Key Points:
- A flaw can cause MFA codes to be logged and potentially leaked.
- Microsoft has released an update to address the issue.
- Users are urged to update the app immediately.
- The vulnerability affects both Android and iOS versions.
Description:
Malwarebytes reports that certain versions of Microsoft Authenticator may inadvertently expose time‑based one‑time passwords, compromising multi‑factor authentication flows for affected users.
Why It Matters:
MFA is a critical line of defense; any leakage of codes can enable credential‑stuffing attacks and unauthorized account access, making rapid patching essential for enterprise security posture.
5️⃣ Android Lock‑Screen Bypass Discovered, Unlocks in ≤60 seconds

Key Points:
- Research shows a flaw allowing lock‑screen bypass in under a minute.
- Exploits leverage race conditions in the biometric subsystem.
- All Android devices with the affected OS version are vulnerable.
- Google has issued a security patch pending rollout.
Description:
A newly disclosed Android vulnerability enables attackers to bypass the device lock screen quickly by exploiting a timing weakness in biometric authentication handling.
Why It Matters:
Compromised mobile devices can expose corporate data, email, and VPN credentials; timely patch deployment is vital to prevent unauthorized data access and lateral movement via mobile endpoints.
6️⃣ OpenClaw AI Skills Weaponized to Deliver Malware at Scale
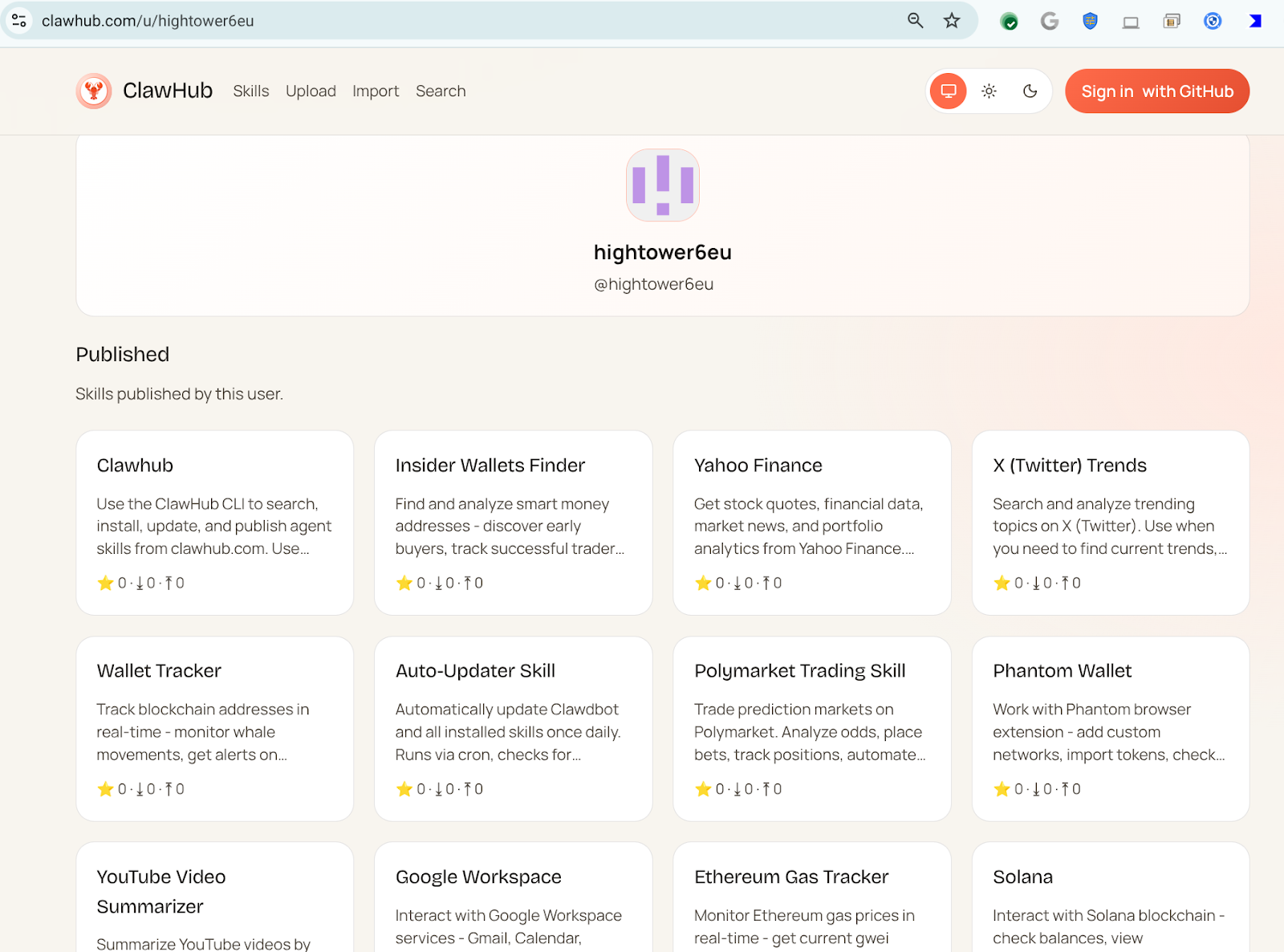
Key Points:
- OpenClaw AI agents are used to automate malicious code downloads.
- A single user, hightower6eu, published over 300 harmful skills.
- Skills masquerade as legitimate utilities such as crypto analytics.
- Execution requires users to run untrusted scripts from the skill.
Description:
VirusTotal analysis reveals that threat actors are publishing malicious OpenClaw AI skills that automate the download and execution of malware under the guise of benign applications.
Why It Matters:
The abuse of AI‑generated automation lowers the barrier for mass malware distribution, demanding new detection strategies for AI‑driven threat vectors in enterprise environments.
7️⃣ OpenClaw AI Advances Include Reverse Shells and Cognitive Rootkits
Key Points:
- Second‑stage OpenClaw skills implement reverse shells for persistence.
- Semantic worms adapt behavior based on target environment.
- Cognitive rootkits employ AI to evade traditional AV signatures.
- Research highlights escalating sophistication of AI‑based attack tools.
Description:
The follow‑up VirusTotal blog details how OpenClaw AI skills have evolved to incorporate reverse shells, adaptive worms, and AI‑powered rootkits that can dynamically modify their code to avoid detection.
Why It Matters:
These capabilities illustrate a shift toward self‑modifying, context‑aware malware, stressing the need for behavioral analytics and AI‑enhanced defenses to counter next‑generation threats.
8️⃣ Research Explores Generalization in Autonomous Cyber‑Attack Agents

Key Points:
- Study evaluates how autonomous agents generalize across attack scenarios.
- Findings show transferability of learned tactics to new targets.
- Implications for both defensive modeling and offensive AI development.
- Proposes benchmarks for future research on AI‑driven cyber attacks.
Description:
An arXiv paper investigates mechanisms that enable autonomous cyber‑attack agents to generalize their behavior, allowing them to adapt tactics when confronting previously unseen environments.
Why It Matters:
Understanding generalization helps defenders anticipate novel attack patterns and develop robust, AI‑informed security controls that can respond to automated adversarial behavior.
9️⃣ ISC Stormcast Highlights Emerging Threat Trends for March 12

Key Points:
- Increased scanning activity on SSH and Telnet ports observed.
- Rise in malicious IP activity targeting IoT device management interfaces.
- New exploit kits leveraging CVE‑2025‑3690 reported.
- Recommendations include network segmentation and updated firmware.
Description:
The Internet Storm Center podcast for March 12 reviewed recent spikes in scanning, IoT‑focused attacks, and emerging exploit kits, offering tactical advice for defenders.
Why It Matters:
Timely awareness of evolving scan patterns and exploit releases enables organizations to harden vulnerable services before attackers can capitalize on them.
🔟 Groundsource Gemini Turns News Into Structured Disaster Data
Key Points:
- Groundsource uses Gemini to convert news narratives into actionable datasets.
- Initial focus on natural‑disaster reporting, with plans for broader hazard types.
- Improves early‑warning capabilities for communities lacking ground‑truth data.
- Open APIs enable integration with emergency‑response platforms.
Description:
Google Research unveiled Groundsource, a system that leverages the Gemini model to extract structured information from news articles, enhancing real‑time situational awareness for disaster response.
Why It Matters:
Accurate, machine‑readable disaster data accelerates coordination among responders and reduces the impact of crises, showcasing how AI can bolster public‑safety intelligence.
Stay vigilant and keep your defenses ahead of the curve.
Member discussion