AI‑driven attack automation escalates supply‑chain risk 🚀. Mobile OS and MFA flaws expose credential theft vectors 🔓.

Good morning, March 12 2026 – here’s the latest intelligence you need.
Today's headlines
- GreyNoise adds real‑time blocklists to Google SecOps and CrowdStrike platforms.
- IoT devices with default admin credentials remain a critical entry point.
- Android lock‑screen flaw can be bypassed in under a minute.
- Microsoft Authenticator may leak one‑time codes to attackers.
- OpenClaw AI skills are being weaponised to deliver malware.
1️⃣ GreyNoise teams with Google SecOps to cut noise
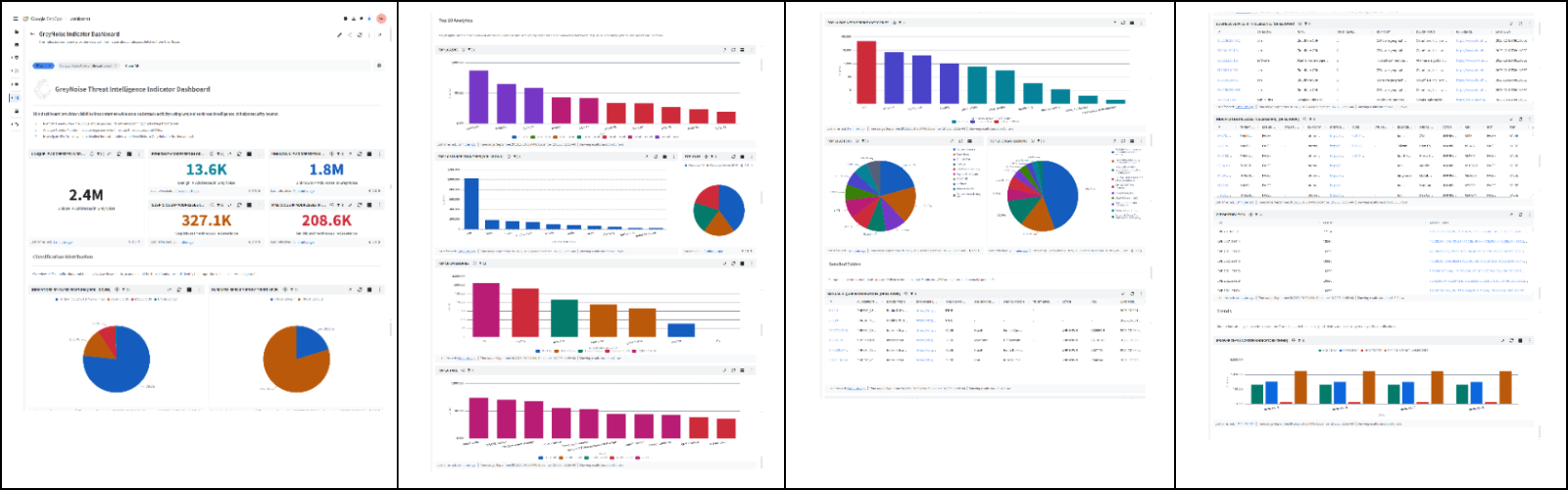
Key Points:
- Integrates GreyNoise intelligence into Google Cloud Security Command Center.
- Provides real‑time blocklists to automatically block malicious IPs.
- Reduces alert fatigue by filtering noisy internet‑scanner traffic.
Description:
GreyNoise announced a native integration with Google SecOps that streams its noisy‑IP intelligence directly into the Cloud Security Command Center, enabling automated blocking of malicious actors and enriching alerts with context about active exploitation trends.
Why It Matters:
For security leaders, the integration promises faster containment of known bad traffic, lower SOC workload, and improved confidence in alert triage, directly supporting risk reduction and operational resilience.
2️⃣ GreyNoise expands to CrowdStrike Falcon platform
Key Points:
- Adds GreyNoise feeds to CrowdStrike Falcon dashboards.
- Enables threat hunting teams to enrich endpoint detections with external IP reputation.
- Supports automated response actions based on internet‑wide scan data.
Description:
GreyNoise intelligence is now available within the CrowdStrike Falcon ecosystem, allowing analysts to overlay internet‑wide scanning data on endpoint alerts, prioritize investigations, and trigger automated block or quarantine actions against compromised IPs.
Why It Matters:
CISOs can leverage this combined visibility to streamline incident response, improve threat‑hunt efficiency, and reduce the time to remediate compromised assets across heterogeneous environments.
3️⃣ IoT admin‑login risk highlighted in SANS diary

Key Points:
- Default admin credentials on IoT devices are still common.
- Attackers can gain persistent network access with a single compromised device.
- Recommendations include MFA, unique passwords, and continuous monitoring.
Description:
A SANS diary entry warns that IoT devices logging in with admin privileges present a critical exposure; once compromised, attackers can pivot to broader network assets, emphasizing the need for strong credentials and device fingerprinting.
Why It Matters:
Enterprise IT leaders must prioritize IoT credential hygiene and monitoring to prevent lateral movement, protecting operational technology and reducing potential breach impact.
4️⃣ Android lock‑screen bypass discovered

Key Points:
- Vulnerability allows bypass of the lock screen within 60 seconds.
- Exploits a flaw in the Android graphics subsystem.
- Patch released, but many devices remain unpatched.
Description:
Malwarebytes reports a critical Android vulnerability that enables an attacker to unlock a device in under a minute by exploiting a graphics driver bug, potentially exposing personal and corporate data on mobile devices.
Why It Matters:
Mobile device security is a top concern for remote workforces; organizations must ensure timely patch deployment and consider mobile device management controls to mitigate data exposure.
5️⃣ Microsoft Authenticator code leak issue

Key Points:
- Bug causes one‑time codes to be logged in plain text.
- Potential for attackers to harvest MFA codes from compromised phones.
- Microsoft has issued an updated app version to fix the issue.
Description:
A flaw in the Microsoft Authenticator app was identified that could inadvertently expose generated login codes, compromising multi‑factor authentication protections until users update to the latest app version.
Why It Matters:
MFA is a cornerstone of identity security; this vulnerability underscores the need for rapid patch management and monitoring of authentication logs for anomalous code usage.
6️⃣ OpenClaw AI skills weaponised for malware delivery
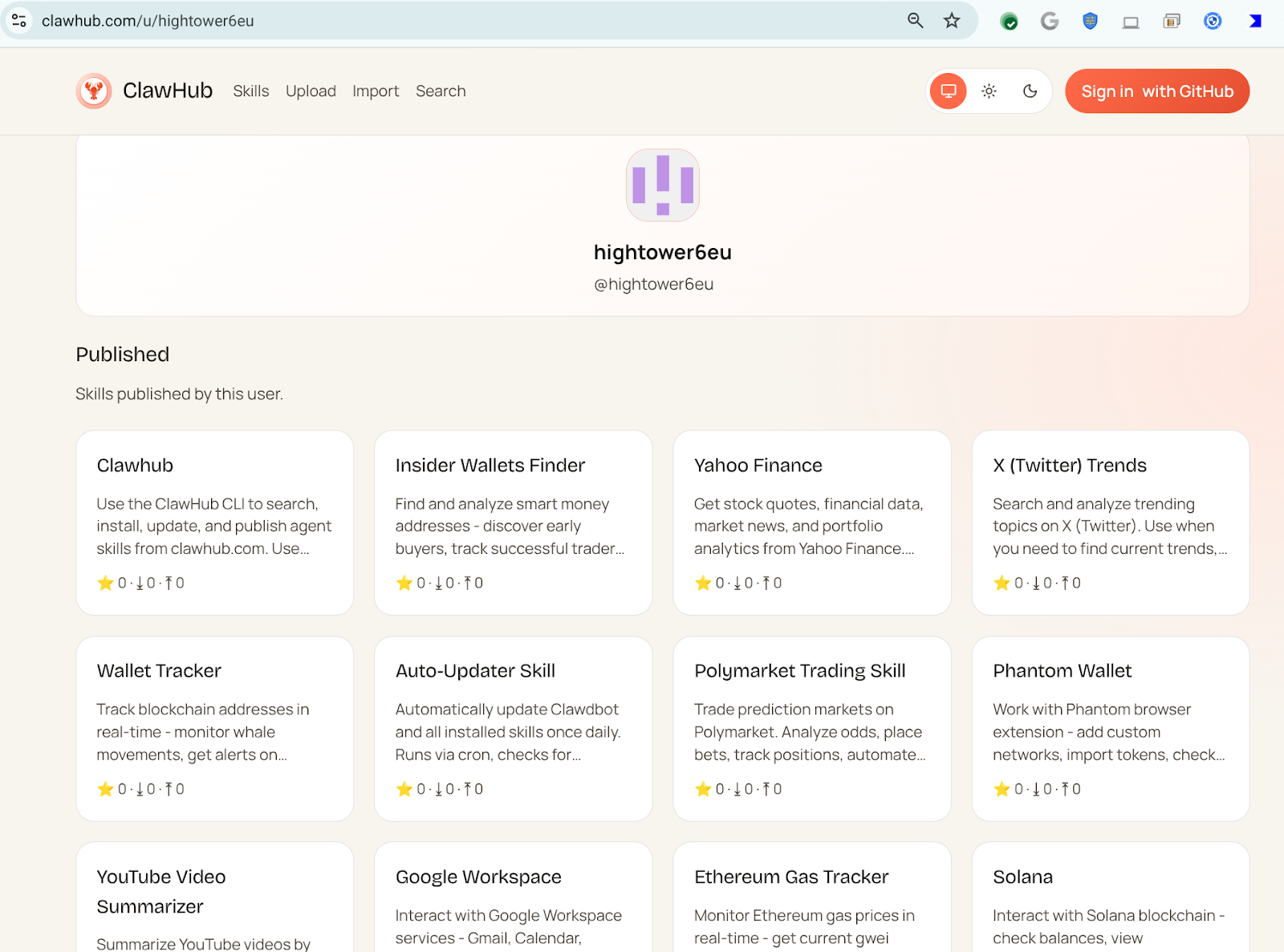
Key Points:
- Threat actor hightower6eu publishes malicious AI skills on OpenClaw.
- Skills disguise malware delivery as legitimate automation tasks.
- Over 300 malicious skill scripts analyzed to date.
Description:
VirusTotal details how a prolific OpenClaw user is publishing AI‑powered automation scripts that appear benign—such as crypto analytics—but install malicious payloads during the setup phase, representing a new supply‑chain attack vector.
Why It Matters:
Enterprises adopting AI automation must validate source integrity and enforce code‑signing policies to avoid inadvertent execution of malicious AI agents.
7️⃣ OpenClaw Part II: Semantic worms and cognitive rootkits
Key Points:
- Advanced OpenClaw skills now deploy reverse shells and self‑modifying code.
- Semantic worms adapt behavior based on environment context.
- Cognitive rootkits can evade traditional endpoint detection.
Description:
The follow‑up VirusTotal analysis uncovers a second wave of OpenClaw AI skills employing reverse shells, semantic worms, and cognitive rootkits that dynamically adjust to evade detection, raising the threat level of AI‑enabled attacks.
Why It Matters:
Security teams need to augment detection frameworks with behavior‑based analytics and restrict AI skill execution to trusted repositories to mitigate these sophisticated threats.
8️⃣ Autonomous cyber‑attack agents evaluated in new arXiv study

Key Points:
- Paper examines generalization mechanisms of AI agents that launch attacks.
- Findings show agents can transfer learned tactics across unseen targets.
- Proposes defensive frameworks to limit autonomous exploit propagation.
Description:
Researchers present a study on autonomous cyber‑attack agents, highlighting their ability to generalize learned exploitation techniques to new environments, and suggesting mitigation strategies such as sandboxing and AI‑focused threat modeling.
Why It Matters:
Understanding the capabilities of self‑learning attack agents helps CISOs prioritize AI‑aware defenses and allocate resources to counter emergent autonomous threats.
9️⃣ ISC Stormcast notes emerging threat trends

Key Points:
- Increase in SSH/Telnet scanning activity across North America.
- Rise in IoT botnet traffic targeting residential routers.
- Recommendations for tightening port filtering and using honeypots.
Description:
The latest ISC Stormcast briefing documents a surge in scanning for weak SSH/Telnet services and expanding IoT botnet activity, providing actionable guidance for network segmentation and detection.
Why It Matters:
Proactive network hygiene, such as limiting exposure of legacy services, reduces the attack surface and aligns with compliance requirements for continuous monitoring.
🔟 Google Groundsource turns news into structured hazard data
Key Points:
- Groundsource uses Gemini AI to extract structured data from news reports.
- Initially focused on natural‑disaster information, expanding to other hazards.
- Aims to improve early‑warning systems for underserved communities.
Description:
Google’s Groundsource project leverages the Gemini model to convert unstructured news articles into machine‑readable datasets, enhancing real‑time situational awareness for natural disasters and potentially other crisis domains.
Why It Matters:
Reliable, AI‑driven hazard data can inform business continuity planning, supply‑chain risk assessments, and insurance underwriting, supporting resilience against emerging physical and cyber‑linked threats.
Stay vigilant and keep your defenses ahead of the evolving threat landscape.
Member discussion