AI‑augmented attacks and new RCE exploit pressure defenses 🛡️. Infrastructure interdependency and regulation intensify 📈.
February 25, 2026 – Daily briefing for security leaders.
Today's headlines
- BeyondTrust RCE vulnerability shows early exploitation activity.
- AI‑augmented threat actors target FortiGate devices at scale.
- GreyNoise report highlights attack concentration and defense gaps.
- CLAIR model maps critical infrastructure interdependencies.
- UK regulators fine adult platforms for child safety violations.
- VirusTotal reveals OpenClaw AI agents weaponizing malware.
1️⃣ BeyondTrust RCE Reconnaissance Reveals Early Exploit Activity
Key Points:
- CVE‑2026‑1731 affects BeyondTrust remote administration tools.
- Scanning activity observed across diverse IP ranges.
- Indicators suggest pre‑emptive exploitation before public disclosure.
- Potential for lateral movement within enterprise networks.
Description:
GreyNoise analysis uncovers reconnaissance patterns linked to the newly assigned CVE‑2026‑1731 RCE in BeyondTrust products. The report details increased probing from multiple threat actors, highlighting automated scans and early‑stage weaponization attempts targeting privileged remote‑admin utilities.
Why It Matters:
An RCE in a widely deployed privileged tool can grant attackers full control over critical systems, amplifying breach impact. Early awareness enables organizations to prioritize patching, strengthen monitoring, and mitigate lateral movement risks before exploit code spreads.
2️⃣ GreyNoise State of the Edge Report Highlights Attack Hotspots

Key Points:
- Concentration of attacks observed in cloud‑edge environments.
- Defensive coverage gaps identified in IoT and remote services.
- Rise in mass‑scanner noise affecting SOC efficiency.
- Recommendations for real‑time blocklists and threat‑intel enrichment.
Description:
The 2026 GreyNoise State of the Edge report analyzes billions of internet‑wide observations, revealing where adversary activity clusters and where defensive controls lag. Findings underscore heightened risk for edge deployments and the need for adaptive, data‑driven blocking strategies.
Why It Matters:
Understanding attack concentration helps CISOs allocate resources to the most exposed assets, improving detection accuracy and reducing false positives. Implementing the report’s suggested blocklists can streamline SOC workflows and close critical security gaps.
3️⃣ Check Point Experts Discuss CTEM vs. Traditional Vulnerability Management

Key Points:
- CTEM integrates threat exposure with asset context.
- Differences highlighted between CTEM and conventional VM processes.
- Practical guidance shared for senior security leaders.
- Emphasis on aligning risk communication across teams.
Description:
In a Reddit AMA, Check Point specialists clarified how Cyber Threat Exposure Management (CTEM) extends beyond classic vulnerability management by correlating exploit likelihood with business impact, offering a more nuanced risk view for decision‑makers.
Why It Matters:
Adopting CTEM can improve prioritization, ensuring that mitigation efforts focus on exposures that matter most to the organization’s mission, thereby enhancing risk‑based resource allocation.
4️⃣ AI‑Augmented Threat Actor Scales FortiGate Compromises

Key Points:
- AI tools automate discovery of vulnerable FortiGate configurations.
- Actors favor softer targets when hardened defenses are met.
- Scale of attacks projected to increase throughout 2026.
- Patch management, credential hygiene, and segmentation emphasized.
Description:
Amazon Threat Intelligence reports a campaign in which AI‑enhanced tooling scans for misconfigured FortiGate firewalls, exploiting weak credentials and outdated firmware to gain footholds across multiple organizations, then shifting focus when defenses improve.
Why It Matters:
The blend of AI efficiency with low‑skill execution lowers the barrier for widespread compromise of perimeter devices, making robust patching and network segmentation essential for maintaining resilient defenses.
5️⃣ CLAIR Model Offers New Framework for Critical Infrastructure Interdependencies
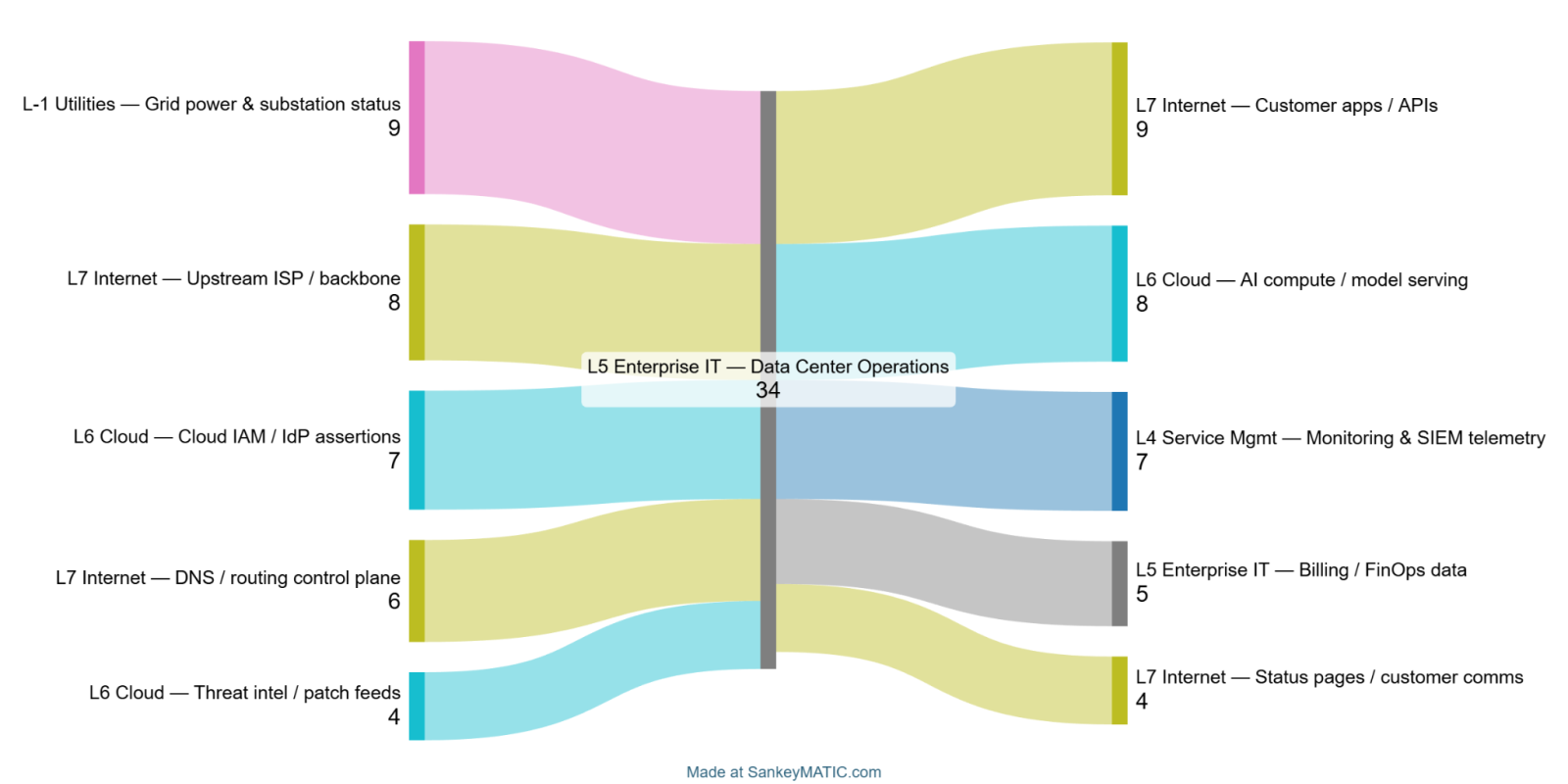
Key Points:
- Synthesizes existing models into a unified interdependency mapping.
- Targets power, water, transport, and communication sectors.
- Provides metrics for cascading failure risk assessment.
- Guides policymakers and operators on resilience planning.
Description:
The CLAIR model, introduced in the SANS diary, integrates concepts from systems‑of‑systems engineering to map how critical infrastructure sectors depend on one another, facilitating analysis of cascading impacts during cyber‑physical events.
Why It Matters:
Understanding interdependencies enables regulators and operators to anticipate indirect effects of attacks, prioritize hardening measures, and improve coordinated response across sectors, thereby reducing systemic risk.
6️⃣ OWASP Announces Retirement of Its Meetup Platform
Key Points:
- Community events will transition to alternative collaboration tools.
- Focus shifts to centralized knowledge bases and virtual workshops.
- Stakeholders advised to migrate memberships and resources.
- Continued commitment to open‑source security education affirmed.
Description:
The OWASP Foundation disclosed that its long‑standing Meetup platform will be retired, prompting the global community to adopt newer platforms for event coordination while maintaining the organization’s emphasis on security best practices and open‑source collaboration.
Why It Matters:
A smooth transition ensures uninterrupted knowledge sharing among developers and security professionals, preserving the ecosystem that fuels vulnerability discovery and remediation across the industry.
7️⃣ UK Regulators Fine Reddit‑Hosted Porn Sites Over Child Safety

Key Points:
- Significant monetary penalties imposed for inadequate age verification.
- Mandates stricter privacy controls for under‑18 users.
- Highlights regulatory focus on online adult content platforms.
- Reddit faces reputational and compliance pressures.
Description:
UK regulators have issued fines against several adult‑content communities hosted on Reddit, citing failures to protect minors’ privacy and ensure robust age‑verification mechanisms, prompting a broader industry discussion on compliance.
Why It Matters:
The enforcement underscores the growing regulatory scrutiny of user‑generated platforms, compelling operators to prioritize child safety features and data protection to avoid legal and reputational fallout.
8️⃣ New App Detects Nearby Smart Glasses to Guard Privacy

Key Points:
- Leverages device sensors to identify AR/VR headsets in proximity.
- Alerts users to potential visual eavesdropping.
- Open‑source implementation encourages community enhancements.
- Addresses emerging privacy concerns in mixed‑reality environments.
Description:
A developer released a mobile application capable of detecting nearby smart glasses using Bluetooth and visual‑signal analysis, providing users with real‑time alerts about possible covert recording devices in their surroundings.
Why It Matters:
As wearable AR devices proliferate, covert surveillance risks increase; tools that surface these threats empower individuals and organizations to safeguard confidential information against visual data leakage.
9️⃣ OpenClaw AI Agent Skills Weaponized for Malware Distribution
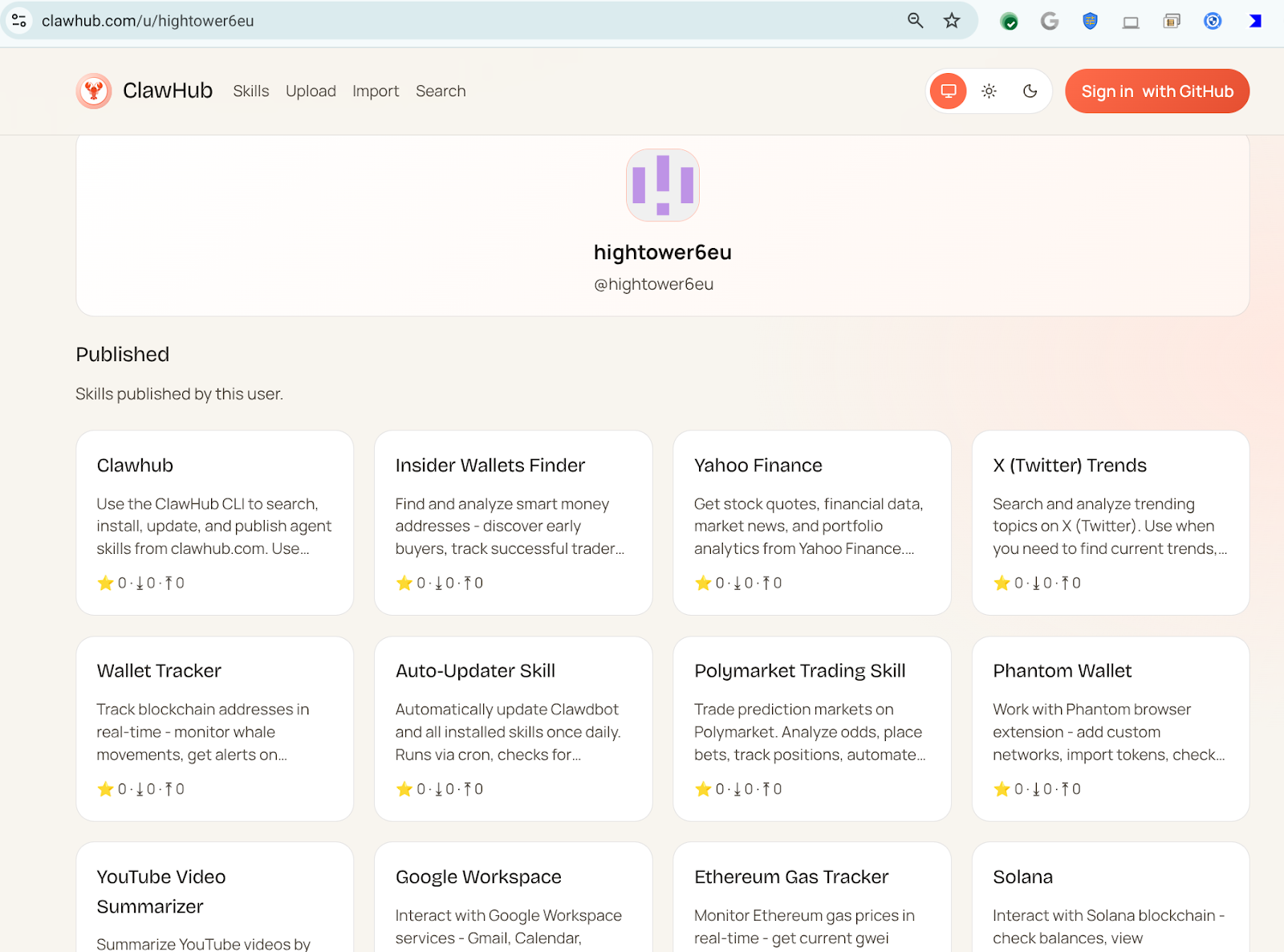
Key Points:
- Malicious actor hightower6eu publishes AI‑generated skills for abuse.
- 314 identified skills used to download and execute untrusted code.
- Skills masquerade as benign utilities (crypto, finance, social media).
- VirusTotal’s Code Insight flags these skills as high‑risk.
Description:
VirusTotal’s research highlights how the OpenClaw AI platform is being exploited by a prolific actor to disseminate malicious skills that appear legitimate but automate the download and execution of payloads, effectively turning automation tools into infection vectors.
Why It Matters:
The abuse of AI‑driven automation blurs the line between benign workflow scripts and malware, demanding updated detection strategies and policy controls for AI skill marketplaces.
🔟 OpenClaw Part II Shows Advanced AI‑Driven Malware Techniques
Key Points:
- Emergence of reverse shells and semantic worms via OpenClaw skills.
- Introduction of cognitive rootkits that adapt to host environments.
- Demonstrates escalation from simple downloaders to persistent threats.
- Calls for AI‑aware threat‑intel and remediation frameworks.
Description:
The follow‑up VirusTotal article delves deeper into OpenClaw’s malicious capabilities, revealing sophisticated AI‑crafted reverse shells, semantic worms, and cognitive rootkits that can persist and evolve within compromised systems, expanding the threat landscape.
Why It Matters:
These advanced AI‑enabled techniques raise the bar for attackers, compelling defenders to develop AI‑centric detection, behavioral analytics, and response playbooks to counter evolving, self‑modifying threats.
Stay vigilant and prioritize resilient controls.
Member discussion