Advanced espionage campaigns and critical zero‑day flaws are reshaping risk landscapes. AI‑powered attacks and supply‑chain compromises demand swift strategic response 🚀🛡️
Feb 12, 2026 – Good morning, security leaders.
Today's headlines
- Amaranth‑Dragon exploits CVE‑2025‑8088 targeting Southeast Asian entities.
- Ivanti EPMM zero‑days leveraged from a single bullet‑proof IP against European agencies.
- LummaStealer evolves with CastleLoader, mimicking legitimate user behavior.
- Notepad++ supply‑chain compromised by nation‑state actors.
- Apple patches a widely‑exploited dyld memory‑corruption zero‑day.
1️⃣ Amaranth‑Dragon weaponizes CVE‑2025‑8088 for Southeast Asian espionage
Key Points:
- APT‑41 linked to the Amaranth‑Dragon campaign.
- Exploits CVE‑2025‑8088 to gain persistent access in targeted networks.
- Focuses on government and critical infrastructure in Southeast Asia.
- Demonstrates a shift toward zero‑day weaponization for strategic espionage.
Description:
Check Point Research identified Amaranth‑Dragon as an advanced persistent threat that has begun weaponizing the newly disclosed CVE‑2025‑8088 vulnerability. The group uses sophisticated delivery mechanisms to infiltrate networks of ministries and energy operators across Southeast Asia, establishing long‑term footholds for intelligence gathering and potential sabotage.
Why It Matters:
Enterprises with operations or supply chains in the region must prioritize rapid patching of CVE‑2025‑8088 and monitor for Indicators of Compromise associated with Amaranth‑Dragon. Failure to remediate exposes critical assets to state‑backed espionage, data exfiltration, and potential disruption of essential services.
2️⃣ Ivanti EPMM exploits traced to a single bullet‑proof IP

Key Points:
- 83% of exploitation attempts originated from IP 193.24.123.42.
- Targets critical CVE‑2026‑1281 and CVE‑2026‑1340 zero‑days in Ivanti EPMM.
- Affected European agencies include the Dutch DPA and Finnish Valtori.
- Exploits provide unauthenticated remote code execution.
Description:
Security researchers observed a concentrated campaign leveraging two critical Ivanti EPMM vulnerabilities. The attacks, emanating from a single hardened IP address, have focused on high‑profile European public sector entities, exploiting CVE‑2026‑1281 and CVE‑2026‑1340 to gain remote code execution without authentication.
Why It Matters:
Organizations using Ivanti EPMM must immediately apply vendor patches and block traffic from the identified IP range. The high success rate of the campaign underscores the urgency of addressing zero‑day exposures to prevent potential compromise of management consoles and downstream systems.
3️⃣ Threat Intel Report: Energy sector hit by ransomware in Romania

Key Points:
- Conpet, Romania’s national oil pipeline operator, suffered a disruptive ransomware attack.
- Attack caused website outage and operational delays.
- Highlights growing targeting of energy infrastructure in Eastern Europe.
- Indicative of coordinated threat actor campaigns against critical utilities.
Description:
The Check Point weekly threat intelligence bulletin detailed a ransomware intrusion against Conpet, the Romanian national oil pipeline operator. Attackers encrypted critical systems, forcing the organization to take its public-facing services offline and disrupting logistical coordination across the national energy grid.
Why It Matters:
The incident emphasizes the heightened risk to energy operators and the need for robust segmentation, continuous monitoring, and rapid incident response capabilities. Executives must reassess supply‑chain resilience and ensure that backup and recovery processes can withstand sophisticated ransomware tactics.
4️⃣ LummaStealer resurfaces with CastleLoader payload integration
Key Points:
- LummaStealer now pairs with CastleLoader to improve stealth.
- Initial access mimics legitimate user behavior and legitimate software.
- Enhanced data exfiltration techniques target financial and credential data.
- Detection requires behavior‑based analytics beyond signature matching.
Description:
Bitdefender researchers observed the evolution of LummaStealer, now leveraging the CastleLoader loader to deliver its payload. The combined operation employs sophisticated social engineering and masquerades as benign processes, making it harder for traditional security tools to detect.
Why It Matters:
Enterprises must augment endpoint detection with user‑behavior analytics to spot anomalous activity that mirrors normal usage. Failure to adapt defenses could result in large‑scale credential theft and financial loss across affected organizations.
5️⃣ Muddled Libra’s operational playbook reveals AI‑enabled extortion tactics

Key Points:
- Group combines PowerShell scripts with AI‑generated phishing content.
- Targets cloud services and cryptocurrency exchanges for credential harvesting.
- Employs DLL sideloading and LLM‑driven social engineering.
- Rapid credential exfiltration leads to accelerated ransomware‑as‑a‑service offers.
Description:
Unit42’s analysis of the Muddled Libra ransomware group shows an advanced playbook that integrates artificial intelligence for crafting convincing phishing emails and automating credential theft. The actors use PowerShell and DLL sideloading to infiltrate cloud environments and quickly monetize stolen data through extortion.
Why It Matters:
Security teams need to implement AI‑aware phishing defenses and tighten cloud access controls. The fusion of AI with traditional ransomware techniques raises the bar for threat detection and necessitates continuous threat‑intel integration.
6️⃣ Notepad++ supply‑chain compromised via malicious update infrastructure

Key Points:
- Nation‑state actors injected malicious code into Notepad++ build pipeline.
- Compromised binaries delivered to millions of developers worldwide.
- Payload includes stealthy backdoor capable of data exfiltration.
- Highlights the risk of trusted open‑source tool supply chains.
Description:
Palo Alto Networks’ Unit 42 uncovered a sophisticated supply‑chain attack on the popular Notepad++ editor. Threat actors infiltrated the build infrastructure, embedding a covert backdoor into official releases that silently collected system information from end users.
Why It Matters:
Enterprises must verify the integrity of open‑source software through reproducible builds and enforce strict application whitelisting. The incident demonstrates that even widely trusted tools can become vectors for large‑scale espionage.
7️⃣ VMware vDefend advances zero‑trust private cloud with lateral movement controls

Key Points:
- vDefend introduces micro‑segmentation and real‑time lateral movement detection.
- Integrates with existing VMware stack for seamless policy enforcement.
- Reduces attack surface across multi‑cloud workloads.
- Provides actionable alerts for anomalous internal traffic.
Description:
VMware’s security blog outlines the latest capabilities of vDefend, a solution designed to strengthen zero‑trust frameworks within private clouds. The platform adds automated micro‑segmentation and continuously monitors lateral movements, enabling rapid containment of threats across heterogeneous environments.
Why It Matters:
CISOs can leverage vDefend to enforce granular network policies, limiting breach propagation and meeting compliance requirements for data isolation. The solution offers a practical path toward comprehensive zero‑trust implementation in complex cloud architectures.
8️⃣ AI simplifies implementation of zero‑trust objectives across enterprise workloads
Key Points:
- Machine‑learning models automate policy generation based on observed traffic patterns.
- Reduces manual configuration errors and speeds up enforcement rollout.
- Integrates with existing security tools for unified visibility.
- Enhances continuous risk assessment and adaptation.
Description:
VMware highlights how artificial intelligence can accelerate the deployment of zero‑trust principles by analyzing network behavior and automatically generating appropriate access policies. The AI‑driven approach minimizes human error and enables dynamic adjustments as environments evolve.
Why It Matters:
Enterprises seeking rapid zero‑trust adoption can benefit from AI‑assisted policy creation, shortening time‑to‑protect and improving overall security posture while conserving resources.
9️⃣ Apple releases patches for exploited dyld zero‑day across all platforms
Key Points:
- Zero‑day CVE‑2026‑20700 in dyld used in targeted attacks.
- Patch delivered for iOS, iPadOS, macOS, tvOS, watchOS, and visionOS.
- Google Threat Analysis Group discovered and reported the flaw.
- Exploitation enables arbitrary code execution via memory corruption.
Description:
Apple issued emergency updates addressing a critical dyld memory‑corruption vulnerability (CVE‑2026‑20700) that had been actively exploited in the wild. The bug allowed attackers with write‑memory capabilities to execute arbitrary code on a broad range of Apple devices.
Why It Matters:
Organizations with Apple device fleets must deploy the updates immediately to prevent remote code execution attacks that could compromise confidential data and enable further malware distribution.
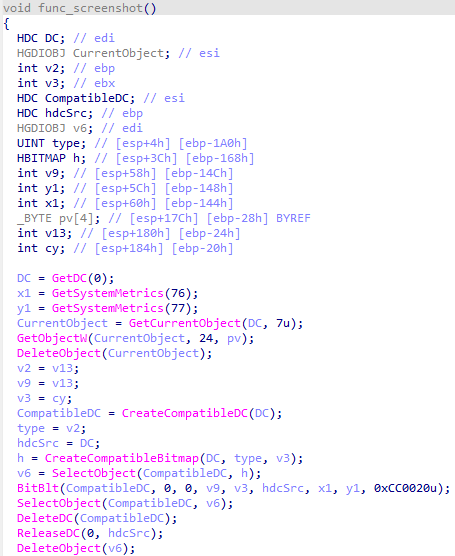
🔟 Kimwolf botnet hijacks I2P anonymity network for large‑scale traffic flooding
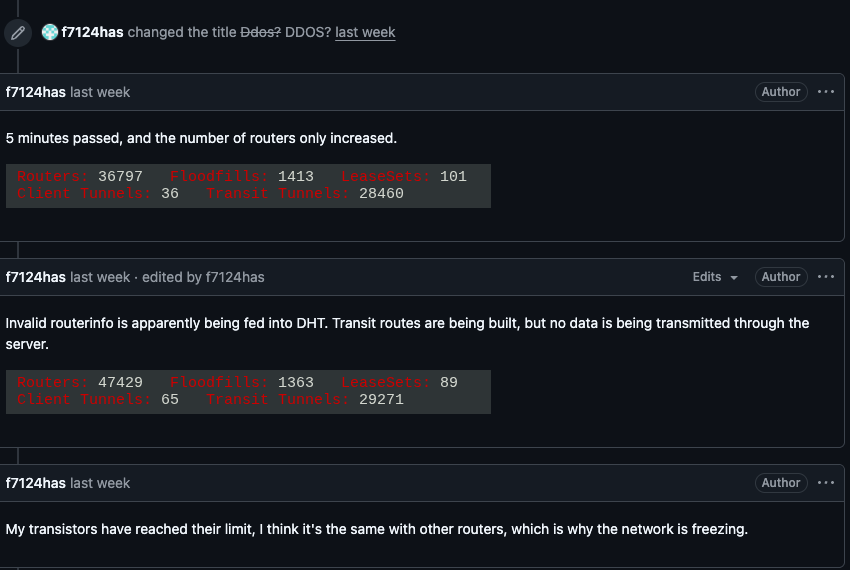
Key Points:
- Botnet leverages compromised hosts to generate massive traffic on I2P.
- Disrupts anonymity services and degrades performance for legitimate users.
- Targets include corporate VPN endpoints and government networks.
- Highlights the abuse potential of privacy‑focused overlay networks.
Description:
KrebsOnSecurity reported that the Kimwolf botnet has begun overwhelming the I2P anonymity network with high‑volume traffic, causing service degradation and potential denial‑of‑service for legitimate users. The botnet’s operators appear to be exploiting the network’s open routing to mask malicious activity.
Why It Matters:
Enterprises relying on privacy networks for secure communications must monitor for abnormal traffic patterns and consider alternative tunneling solutions. The incident underscores the need for robust network monitoring to detect and mitigate botnet‑driven abuse.
Stay vigilant and act decisively to protect your organization.
Member discussion