Advanced APT weaponization escalates espionage risks across Southeast Asia 🚀. Simultaneously, AI‑driven and supply‑chain attacks strain enterprise resilience 🛡️.
Good morning, February 12, 2026. Below are the critical threats demanding executive attention this week.
Today's headlines
- APT groups weaponize newly disclosed CVEs to infiltrate Southeast Asian targets.
- AI-driven exploits and 0‑click attacks become mainstream, increasing persistence.
- Critical infrastructure in Europe suffers disruptive cyberattacks, highlighting sector risk.
- Supply chain compromises of popular developer tools expose wide user base.
- Human‑AI feedback loops advance detection of zero‑day threats.
1️⃣ Amaranth-Dragon Exploits CVE‑2025‑8088 for Southeast Asian Espionage
Key Points:
- Targets government and telecom entities in Southeast Asia.
- Leverages CVE‑2025‑8088 to gain persistent footholds.
- Linked to APT‑41 activity and supply‑chain abuse.
Description:
Checkpoint researchers identified the Amaranth-Dragon group weaponizing the newly disclosed CVE‑2025‑8088 vulnerability to conduct targeted espionage campaigns against Southeast Asian organizations. The actors deployed custom malware that exploits the flaw to establish long‑term access, masking their presence within legitimate network traffic.
Why It Matters:
The exploitation of a fresh zero‑day underscores the urgency for rapid patch management and threat‑intel integration. Organizations in the region must reassess their exposure to kernel‑level flaws and strengthen detection capabilities to prevent clandestine data exfiltration.
2️⃣ AI‑Powered Prompt RCE and 0‑Click Attacks Surge in ThreatsDay Bulletin

Key Points:
- AI‑generated prompts trigger remote code execution without user interaction.
- Claude 0‑click exploit demonstrates automated weaponization of language models.
- RenEngine loader used to deliver multiple zero‑day payloads.
Description:
The ThreatsDay Bulletin highlighted a wave of AI‑driven attacks, including a prompt‑based remote code execution vulnerability and a 0‑click exploit targeting the Claude AI model. Attackers also employed the RenEngine loader to silently deploy new zero‑day exploits, indicating a shift toward leveraging trusted tools for high‑impact intrusion.
Why It Matters:
These developments reveal that adversaries can now automate exploit delivery at scale, reducing detection windows. Enterprises must implement AI‑aware security controls and monitor for abnormal tool usage to mitigate these emerging vectors.
3️⃣ Conpet Oil Pipeline Disruption Highlights Critical Infrastructure Vulnerability

Key Points:
- Romanian national oil pipeline operator Conpet suffered a cyberattack.
- Attack disrupted IT systems and took the company website offline.
- Potential impact on fuel distribution and regional energy security.
Description:
Checkpoint’s weekly threat intelligence report noted that Conpet, Romania’s national oil pipeline operator, experienced a cyberattack that crippled its internal IT environment and rendered its public website inaccessible. While the exact intrusion method remains under investigation, the incident illustrates the vulnerability of critical energy infrastructure to sophisticated threats.
Why It Matters:
Disruption of essential services can cause cascading economic effects and erode public trust. Energy sector leaders must prioritize network segmentation, incident response readiness, and continuous monitoring to safeguard operational continuity.
4️⃣ Nation‑State Compromise of Notepad++ Supply Chain Undermines Developer Trust

Key Points:
- Supply‑chain attack inserted malicious code into Notepad++ updates.
- Threat actors leveraged the popular editor to reach a broad user base.
- Palo Alto Networks coordinated with CTA members for rapid mitigation.
Description:
Palo Alto Networks’ Unit 42 disclosed that nation‑state actors compromised the Notepad++ software supply chain, embedding malicious code into legitimate updates distributed to millions of developers worldwide. The malicious payload was designed to establish persistence on victim machines and exfiltrate data silently.
Why It Matters:
Compromise of widely trusted development tools expands the attack surface across organizations of all sizes. Software vendors and users must enforce code‑signing verification, implement strict update validation, and collaborate through alliances like the CTA to quickly respond to such threats.
5️⃣ CrowdStrike’s Human‑AI Feedback Loop Elevates Agentic Security Posture
Key Points:
- Integrates human analyst insights with AI models for continuous learning.
- Identified and helped patch six zero‑day vulnerabilities in early 2026.
- Improves detection of AI‑generated phishing and data‑leak attempts.
Description:
CrowdStrike revealed its human‑AI feedback loop architecture, where analyst‑driven context refines machine‑learning models to better detect emerging threats. This approach enabled the rapid identification and remediation of six zero‑day flaws, reinforcing the company’s agentic security framework.
Why It Matters:
Combining human expertise with AI accelerates threat detection cycles, granting organizations a proactive edge against sophisticated adversaries. Enterprises should consider adopting similar feedback mechanisms to keep defenses aligned with evolving attack techniques.
6️⃣ Falcon Fusion SOAR Scales SOC Automation for Faster Incident Response
Key Points:
- Provides low‑code playbooks for common attack scenarios.
- Reduces mean time to response (MTTR) by up to 60%.
- Integrates with existing security stacks for unified workflow.
Description:
CrowdStrike introduced Falcon Fusion SOAR, a platform that enables security operations centers to automate response playbooks with minimal coding effort. By orchestrating alerts across multiple tools, the solution shortens investigation cycles and streamlines containment actions.
Why It Matters:
Automation mitigates analyst fatigue and limits dwell time, key factors in limiting breach impact. Organizations seeking to scale SOC capabilities should evaluate SOAR solutions that align with their existing technology ecosystem.
7️⃣ VMware vDefend Lateral Security Advances Zero‑Trust Private Cloud

Key Points:
- Detects lateral movement across micro‑segmented workloads.
- Leverages AI to prioritize high‑risk alerts in private clouds.
- Supports seamless integration with existing VMware infrastructure.
Description:
VMware’s vDefend Lateral Security component adds AI‑driven detection of suspicious lateral activity within private cloud environments. The solution extends zero‑trust principles by continuously validating inter‑workload communications and flagging anomalous behavior.
Why It Matters:
As enterprises migrate workloads to private clouds, unchecked lateral movement can facilitate deep compromises. Leveraging AI for real‑time risk triage helps security teams focus on the most critical threats, reinforcing a robust zero‑trust posture.
8️⃣ Meta Faces Trial Over Child Exploitation Claims, Raising Platform Accountability

Key Points:
- Legal case examines Meta’s role in child grooming and exploitation.
- Highlights need for stronger moderation and safety mechanisms.
- Industry scrutiny intensifies around social‑media security responsibilities.
Description:
A high‑profile trial is challenging Meta over alleged child exploitation, grooming, and social‑media addiction claims. The proceedings focus on whether the platform’s safety systems adequately prevent harmful interactions and protect vulnerable users.
Why It Matters:
Regulatory and legal pressures are mounting on social‑media providers to enforce stricter safeguarding measures. Enterprises must monitor policy changes that could affect data handling, content moderation, and broader cybersecurity compliance obligations.
9️⃣ AI Simplifies Zero‑Trust Implementation, Boosting Policy Automation

Key Points:
- AI automates policy generation based on real‑time risk assessments.
- Reduces manual configuration errors in access controls.
- Accelerates adoption of zero‑trust across hybrid environments.
Description:
VMware’s recent blog outlines how artificial intelligence can streamline the rollout of zero‑trust security by automatically generating and adjusting access policies according to observed behavior and threat intelligence. The approach minimizes human error and speeds up compliance.
Why It Matters:
Simplified policy automation enables faster, more consistent enforcement of zero‑trust principles, crucial for protecting complex, multi‑cloud ecosystems. Organizations should explore AI‑enabled policy engines to reduce operational overhead and improve security posture.
🔟 Kimwolf Botnet Exploits I2P Anonymity Network, Amplifying DDoS Risks
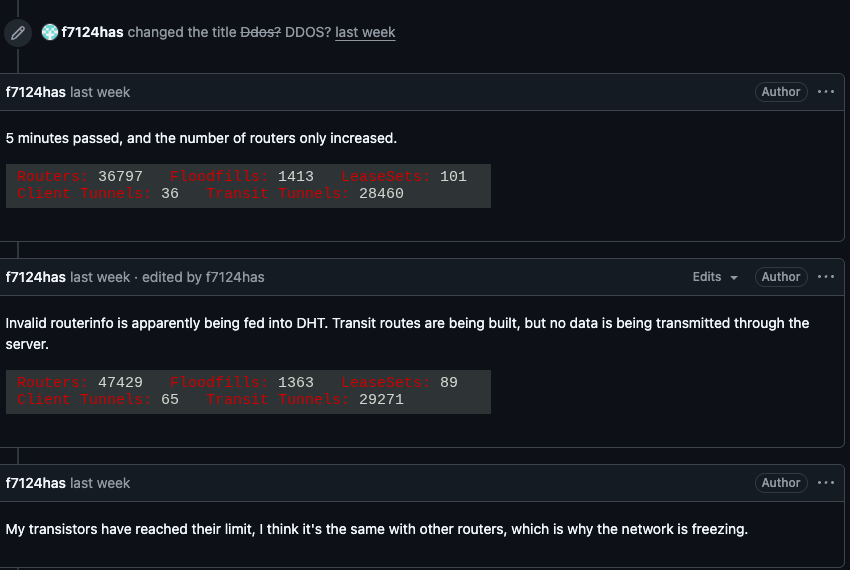
Key Points:
- Botnet leveraged I2P to hide command‑and‑control traffic.
- Generated large‑scale DDoS attacks against multiple targets.
- Highlights challenges in detecting abuse within anonymity networks.
Description:
KrebsOnSecurity reported that the Kimwolf botnet has begun using the I2P anonymity network to conceal its command‑and‑control infrastructure, enabling it to launch high‑volume distributed denial‑of‑service attacks while evading typical detection methods.
Why It Matters:
The use of privacy‑preserving networks for malicious purposes complicates traditional network monitoring. Defenders must adopt advanced traffic analysis and collaborate with anonymity network operators to mitigate such hidden threats.
Stay vigilant and prioritize proactive defenses.
Member discussion